About 3 million already carry out their tasks remotely, which represents 74.2% more teleworkers than before the pandemic. But how do you protect organizations and their professionals in a hybrid work environment? Defining adequate security policies, along with the implementation of tools and training, are essential.
Hybrid environments in which employees divide their day between the office and their home pose a new challenge for companies: securing these new work environments.
By analyzing the main security breaches of the last two months, Proofpoint researchers have identified what attacks can look like in these hybrid environments. In this sense, the connection to corporate networks with tighter controls and the jump to home networks, the sharing of devices for work and personal activities or the use of company equipment by other family members are some of the causes of reduced security. To this is added that the behavior of employees has changed, as well as the way of working as a team, and more people have been joining them who previously did not enter the equation. To alleviate this, there are five points that those responsible for cybersecurity in Spanish companies should focus on:
Device configuration on the network. After more than a year connected to home networks, it is crucial to manage the vulnerabilities of the devices and analyze their security completely to ensure that they are clean before reconnecting them to the corporate network. This can prevent potential malware infections that could compromise your organization’s systems. A great effort must be made in asset management, control and reconfiguration, as well as checking that all devices are patched and updated.
Analyze employee behavior and define new policies. Typically, users have relaxed their security habits, which requires more efforts to retrain them and reinforce “good” practices. You need to define what’s good in this new hybrid world, and then underpin these concepts with a security awareness that is tailored to the behaviors.
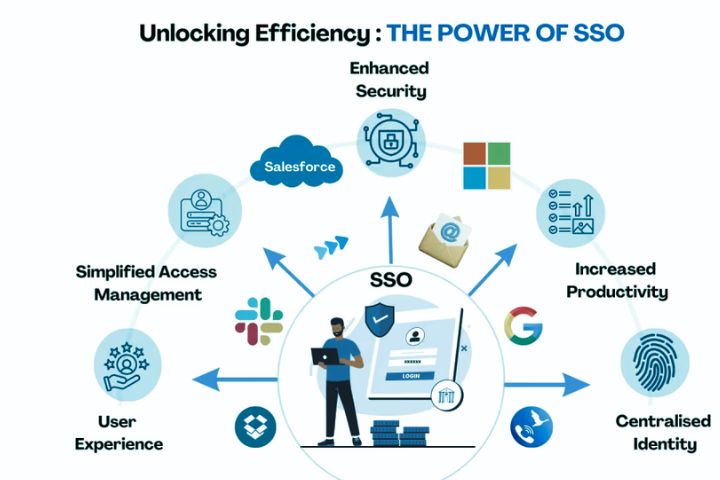
Maintain collaboration. Although email continues to be the main communication channel between employees and with third parties, users have started to use more and more telecommunications services that were not common in the day-to-day business of the company. Collaboration tools are a very easy target for spreading malware across an organization, even in this hybrid work environment. Any new channel, application or service can become an attack vector, so they must be known and protected.
The same threats for many targets. People are still the main target of cybercriminals. As a study by Verizon shows, the most used tactic in the attacks was phishing (35%), and the human factor was key in 85% of the attacks. A single click is enough for the success of a cyberattack, and that click can happen in the office, at home or on the go. In addition, user data and passwords provide access to data that is increasingly moving to the cloud. In fact, credentials were used in 61% of the incidents in the past year.
New faces, new threats. The incorporation of new professionals also carries security risks. Their own situation makes them easy targets for social engineering: they don’t know all of their peers yet, they probably haven’t received security training from the organization, and they’re eager to please.









![TamilRockers Proxy 11 Mirror-Sites [Updated 2022] & How to Unblock It](https://www.techsplashers.com/wp-content/uploads/2022/01/TamilRockers-Proxy-11-Mirror-Sites-Updated-2022-How-to-Unblock-It.jpg)
Leave a Reply